Let's be blunt: skipping out on incident response planning is a gamble you can't afford to take. A well-documented data breach response plan isn't just about ticking a compliance box. It's a fundamental part of your business continuity, protecting your bottom line, your reputation, and your company's future from the very real damage a breach can inflict.
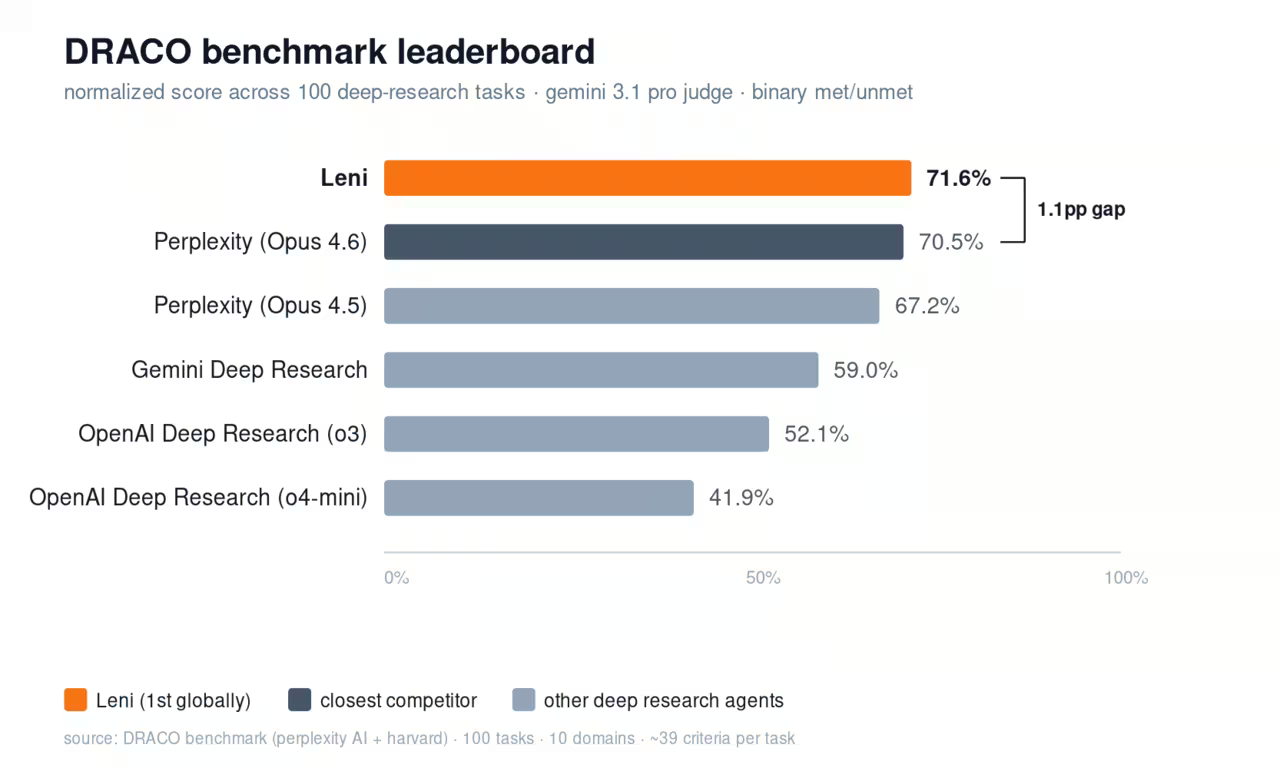
- The global average cost of a data breach reached $4.88 million in 2024, a 10% increase year-over-year (IBM Cost of a Data Breach Report 2024).
- Organizations with a tested incident response plan saved an average of $1.49 million per breach compared to those without one (IBM).
- The average breach lifecycle from identification to containment is 277 days, with malicious attacks averaging 322 days (IBM 2023).
- Only 35% of SMBs have a formal, documented data breach response plan in place (Hiscox Cyber Readiness Report 2024).
The Real Cost of Being Unprepared
Too many businesses see incident response planning as a cost center, not an investment. This is a critical mistake. The reality is that the staggering costs of a poorly managed security incident dwarf the resources needed to prepare for one. We're not talking about theoretical risks; these are hard, quantifiable numbers from recent industry reports.
The consequences are stark. According to IBM's Cost of a Data Breach Report, organizations with a high level of incident response planning and testing saved an average of $1.49 million compared to those with no plan. That's a direct financial incentive for preparedness. Ponemon Institute research further confirms that companies with an established incident response team reduce breach costs by an average of $340,000 per incident, largely through faster containment and reduced regulatory exposure.
It gets worse. The same report found that the average lifecycle of a data breach--from identification to containment--was 277 days. For breaches caused by a malicious attack, that number jumps to 322 days. That's nearly a year where an attacker could be active in your network. Verizon's 2024 Data Breach Investigations Report (DBIR) found that 68% of breaches involved a human element, whether through social engineering, credential theft, or simple errors--making preparation and training even more critical.
At a Glance: The Costs of Unpreparedness
This table breaks down just how much a lack of preparation can hurt. The numbers show a clear pattern: proactive planning directly translates to faster recovery and lower financial impact.
| Metric | With High IR Planning/Testing | Without IR Planning/Testing | Cost/Time Impact |
|---|---|---|---|
| Breach Lifecycle | 253 Days | 305 Days | 52 extra days of compromise |
| Average Breach Cost | $3.96 Million | $5.45 Million | $1.49 Million Higher |
| Response Time | Hours/Days | Weeks/Months | Slower containment, more damage |
| Customer Trust | Retained with swift action | Severely eroded | Long-term revenue loss |
| Regulatory Fines | Minimized through compliance | Severe penalties likely | GDPR fines up to 4% of global revenue |
As you can see, the time and money lost from a reactive, chaotic approach can be devastating. A documented plan is your financial and operational lifeline.
"Incident response planning is not a one-time exercise but a continuous process of improvement. The organizations that recover fastest from breaches are those that have rehearsed their response plan so thoroughly that execution becomes second nature under pressure."
-- Chris Krebs, Former Director of the Cybersecurity and Infrastructure Security Agency (CISA)
Beyond the Initial Financial Hit
The damage doesn't stop with the initial cleanup bill. A mismanaged breach sets off a chain reaction of secondary costs that can hamstring your business for years. According to a Deloitte study, the "hidden costs" of a data breach--including intellectual property loss, devaluation of brand, and operational disruption--can be 5 to 10 times higher than the direct costs that are typically reported.
- Erosion of Customer Trust: When customers feel their data is at risk, they walk. A PwC survey found that 87% of consumers say they will take their business elsewhere if they feel a company doesn't handle their data responsibly. Rebuilding that trust takes years of hard work and significant marketing spend.
- Operational Disruption: System downtime isn't just an IT problem. The Ponemon Institute estimates that the average cost of IT downtime is approximately $9,000 per minute for large enterprises. It means stalled projects, diverted resources, and a complete halt to business momentum while everyone shifts into crisis mode.
- Regulatory Penalties: Regulators don't mess around. GDPR fines can run up to 4% of global annual revenue or 20 million euros, whichever is greater. In 2023, Meta was fined a record $1.3 billion for GDPR violations. These are blows that can be especially crippling for small and mid-sized businesses.
- Stock Price Impact: For publicly traded companies, Comparitech research shows that breached companies underperform the NASDAQ by an average of -3.5% in the six months following public disclosure of the incident.
One often-overlooked area that contributes to these costs are new data breaches from improper equipment disposal. It's a simple mistake with massive consequences.
A Framework for Resilience
Ultimately, a data breach response plan is your framework for resilience. It ensures that when an incident hits, your team acts with precision, not panic. Every minute you save during a breach directly cuts costs and minimizes the hit to your reputation. The SANS Institute emphasizes that organizations should aim to move from detection to containment within one hour for critical incidents--a goal that is only achievable with a pre-rehearsed plan.
Having a clear chain of command, pre-approved communications, and established containment procedures prevents the frantic, ill-advised decisions that often make a bad situation much worse. This proactive approach, which should always include robust backup solutions, turns a potential catastrophe into a manageable event. If you're exploring options, you might find our review of IDrive useful. You can check it out at https://dupple.com/tools/idrive.
Putting Together Your Data Breach Response Team
Let's be honest: your data breach response plan is just a document until you have the right people ready to bring it to life. When a real crisis hits, there's zero time to start figuring out who's in charge of what. Building your Data Breach Response Team (DBRT) ahead of time is the single biggest factor that separates a controlled, effective response from absolute chaos.
Think of it like an emergency room. Everyone has a specific job, they know exactly what to do, and they know who to talk to. Without that structure, the patient--in this case, your business--is in serious trouble. Gartner research indicates that organizations with a formally designated incident response team reduce the average cost of a breach by $250,000 or more, largely because pre-assigned roles eliminate the confusion and delays that inflate costs during the critical first hours.
Data Breach Response Team (DBRT) Role Assignment Template
Use this template to document your team. Fill in names, contact details, and backup personnel for each role. Review and update quarterly.
| Role | Primary | Backup | 24/7 Contact | Key Responsibilities |
|---|---|---|---|---|
| Incident Commander | [Name] | [Name] | [Phone/Signal] | Overall coordination, executive decisions, status briefings |
| IT Forensics Lead | [Name] | [Name] | [Phone/Signal] | Technical investigation, evidence preservation, containment |
| Legal Counsel | [Name] | [External Firm] | [Phone/Email] | Regulatory compliance, notification requirements, evidence handling |
| Communications Lead | [Name] | [Name] | [Phone/Email] | Internal/external messaging, media relations, customer notices |
| Customer Support Lead | [Name] | [Name] | [Phone/Email] | Support team briefing, FAQ preparation, customer escalation handling |
| HR Representative | [Name] | [Name] | [Phone/Email] | Employee communication, insider threat coordination, staff well-being |
| External DFIR Vendor | [Firm Name] | [Alt Firm] | [Retainer Hotline] | On-call forensic investigation, malware analysis, expert testimony |
Tip: Keep a printed copy of this table in a physical binder stored offsite. During a breach, your email and internal systems may be compromised--you need contact information accessible outside your network.
Who Needs to Be on the Team?
A solid DBRT isn't just an IT-only club. The shockwaves from a breach travel through every part of your company, so you need a mix of technical know-how, legal guidance, and communications savvy. Simply assigning this to the "IT department" is a recipe for disaster. You need specific people with clearly defined responsibilities.
Your team should pull in key people from across the organization, each ready to jump into action. This ensures you're covering all your bases, from shutting down the technical threat to keeping your customers in the loop. According to the SANS Institute, organizations that include cross-functional members on their response team reduce mean time to containment by an average of 27% compared to IT-only teams.
Here are the non-negotiable roles you need to fill:
- Incident Commander (The Quarterback): This is the single person calling the shots and coordinating the entire response. They aren't necessarily the one in the weeds fixing the technical issue; their job is to direct the team, make the tough calls, and keep leadership informed. They manage the crisis, not the code.
- Forensics and IT Security Lead (The Detective): This is your boots-on-the-ground technical expert. They're responsible for digging in to find out how the breach happened, figuring out what was taken, stopping the bleeding, and kicking the attackers out of your systems for good.
- Legal Counsel (The Navigator): Get them involved from minute one. This person is your guide through the labyrinth of legal and regulatory requirements. They'll advise on who you need to notify and when (think GDPR, CCPA), handle potential lawsuits, and make sure any evidence is collected properly. The International Association of Privacy Professionals (IAPP) notes that over 140 countries now have data protection legislation, making legal coordination essential for any business operating across borders.
- Communications Lead (The Spokesperson): This individual owns the story. They manage every message that goes out, both internally to employees and externally to customers and the press. Their goal is to maintain a consistent, transparent, and calm voice throughout the storm.
- Customer Support Lead (The Front Line): This is the person who gets your support team ready for the flood of calls and emails from worried customers. They arm their agents with approved talking points and FAQs to help maintain customer trust when it matters most.
Seeing the Team in Action: A Ransomware Scenario
Picture this: you walk in Monday morning and every critical server is locked down with a ransom note on the screen. Sophos' 2024 State of Ransomware report found that the average ransom payment reached $2.73 million in 2024--a 500% increase from 2023. This is where your pre-defined team proves its worth.
The Incident Commander immediately gets the DBRT together, sets up a "war room" (physical or virtual), and establishes a secure way to communicate. Their first order is simple: confirm what's happening and figure out how badly business operations are hit.
At the exact same time, the IT Forensics Lead is already working to isolate the infected systems to keep the ransomware from spreading further. They're digging through logs to find the point of entry while carefully preserving digital evidence. Containment is everything in these first few minutes.
If there's one principle to remember, it's clarity. In the middle of a high-stress incident, ambiguity is your worst enemy. A clear chain of command gets you decisive action, stops people from stepping on each other's toes, and speeds up the entire response.
While the tech team is fighting the fire, Legal Counsel is already figuring out notification deadlines based on the kind of data that might have been compromised. They're also advising the Incident Commander on the risks and legalities of even considering paying the ransom. The FBI's Internet Crime Complaint Center (IC3) strongly recommends never paying a ransom, as it funds criminal operations and does not guarantee data recovery--with only 65% of data being recovered on average even after payment. Meanwhile, the Communications Lead is quickly drafting an internal message for all employees to stop rumors from flying.
As the technical team works on recovery options, the Customer Support Lead is prepping their agents for the questions they know are coming. This kind of coordinated, multi-front response is only possible because everyone knew their role long before the attack ever happened. For any business serious about building this kind of resilience, it's worth looking at specialized platforms that can help. You can learn more about how tools like CyberUpgrade can help protect your organization.
Navigating the Four Phases of Incident Response
When you're hit with a data breach, it's not a single moment of chaos--it's a process. A well-oiled response isn't about one frantic action; it's a structured lifecycle that helps your team move with precision instead of panic. This process is almost universally broken down into four distinct phases, each with its own mission-critical goals. The framework is based on the NIST Computer Security Incident Handling Guide (SP 800-61 Rev. 2), which remains the gold standard for organizations of every size.
Think of this framework less like a rigid checklist and more like a strategic map. It's what guides you from being prepared before an incident to emerging stronger and more resilient after one. Getting a handle on these phases is the first real step in building a data breach response plan that actually works when you need it most.
The First Phase: Preparation
This is, hands down, the most important part of incident response, and it all happens long before anything goes wrong. Preparation is all about laying the groundwork so you can react swiftly and in an organized way. If you skip this, the other phases will be chaotic, messy, and a whole lot more expensive. The Ponemon Institute found that organizations in the "prepared" category spend an average of $2.46 million less on breach-related costs than their unprepared counterparts.
This proactive stage is built on a few key activities:
- Risk Assessments: You can't protect what you don't know you have. This means getting a firm grasp on your most critical data, figuring out where it lives, and understanding the real-world threats it faces. The National Institute of Standards and Technology (NIST) recommends conducting formal risk assessments at least annually, or whenever significant changes occur to your IT environment.
- Deploying Security Tools: This is your technical foundation. We're talking about setting up firewalls, having solid endpoint detection and response (EDR) systems in place, and using security information and event management (SIEM) solutions to keep an eye on everything. Gartner predicts that by 2027, 75% of organizations will consolidate security vendor count to three or fewer integrated platforms.
- Training Your Team: Your people are your first line of defense. Regular, practical training on security hygiene and how to spot phishing attacks can stop a huge number of incidents before they even begin. The SANS Institute recommends conducting security awareness training at minimum twice per year, with simulated phishing exercises monthly.
The real goal of preparation isn't just to stop incidents. It's to build the muscle memory, have the tools ready, and drill the processes so that when something inevitably does happen, your organization can manage it effectively.
The Second Phase: Detection and Analysis
This phase kicks into high gear the second a potential security event is flagged. The mission here is twofold: figure out if a breach actually happened and, if so, understand its nature and initial impact. Speed and accuracy are everything at this stage.
The big challenge is that attackers are sneaky and can hide in a network for months. The average time to identify a breach in 2023 was 204 days, with another 73 days to contain it. That means an attacker could have free rein for over nine months before being stopped. Mandiant's M-Trends 2024 report shows a slight improvement, with the global median dwell time dropping to 10 days for incidents detected by external parties--but only for organizations with mature detection capabilities.
Once an alert goes off, your team has to jump on it:
- Validate the Incident: Not every blip on the radar is a five-alarm fire. The first step is to quickly confirm if you're looking at malicious activity or just a false positive. Gartner estimates that security teams waste up to 25% of their time chasing false positives, making efficient triage essential.
- Determine the Scope: Analysts then dig in to figure out which systems are hit, what user accounts might be compromised, and what the attacker is actually doing.
- Assess the Severity: Based on the findings, the team has to prioritize the incident. This is all about its potential impact on business operations, the sensitivity of the data involved, and any regulatory clocks that are now ticking.
The Third Phase: Containment and Eradication
Okay, you've confirmed a breach and have a sense of its scope. Now, the immediate priority is to stop the bleeding. The containment phase is all about isolating the affected systems to prevent the attacker from digging deeper into your network and doing more damage.
This is a delicate balancing act. You have to move fast, but you also have to be careful to preserve evidence for the forensic investigation that will follow. Common moves here include yanking compromised servers offline, segmenting parts of the network, or blocking malicious IP addresses at the firewall. CrowdStrike's 2024 Global Threat Report emphasizes that adversary breakout time--the time it takes an attacker to move laterally from initial access--has dropped to an average of just 62 minutes, making speed-to-containment absolutely critical.
Once the threat is boxed in, the focus shifts to eradication--getting the threat completely out of your environment. This is way more than just deleting a malicious file. It means:
- Removing Malicious Code: Making sure every last trace of the attacker's tools is scrubbed.
- Patching Vulnerabilities: Closing the security hole the attacker used to get in in the first place.
- Resetting Credentials: Forcing password changes for all compromised accounts and disabling them until they're clean.
- Validating Eradication: Running complete scans with updated signatures to confirm no persistence mechanisms remain. The MITRE ATT&CK framework documents over 200 persistence techniques that attackers commonly use.
Just restoring from a backup without getting to the root cause is a surefire way to get hit again. And speaking of backups, it's essential to have secure ones from the start. We did a deep dive on Tresorit, a tool that can be a big help in securing sensitive company data.
This process highlights the core roles that have to sync up during these intense phases of a data breach.
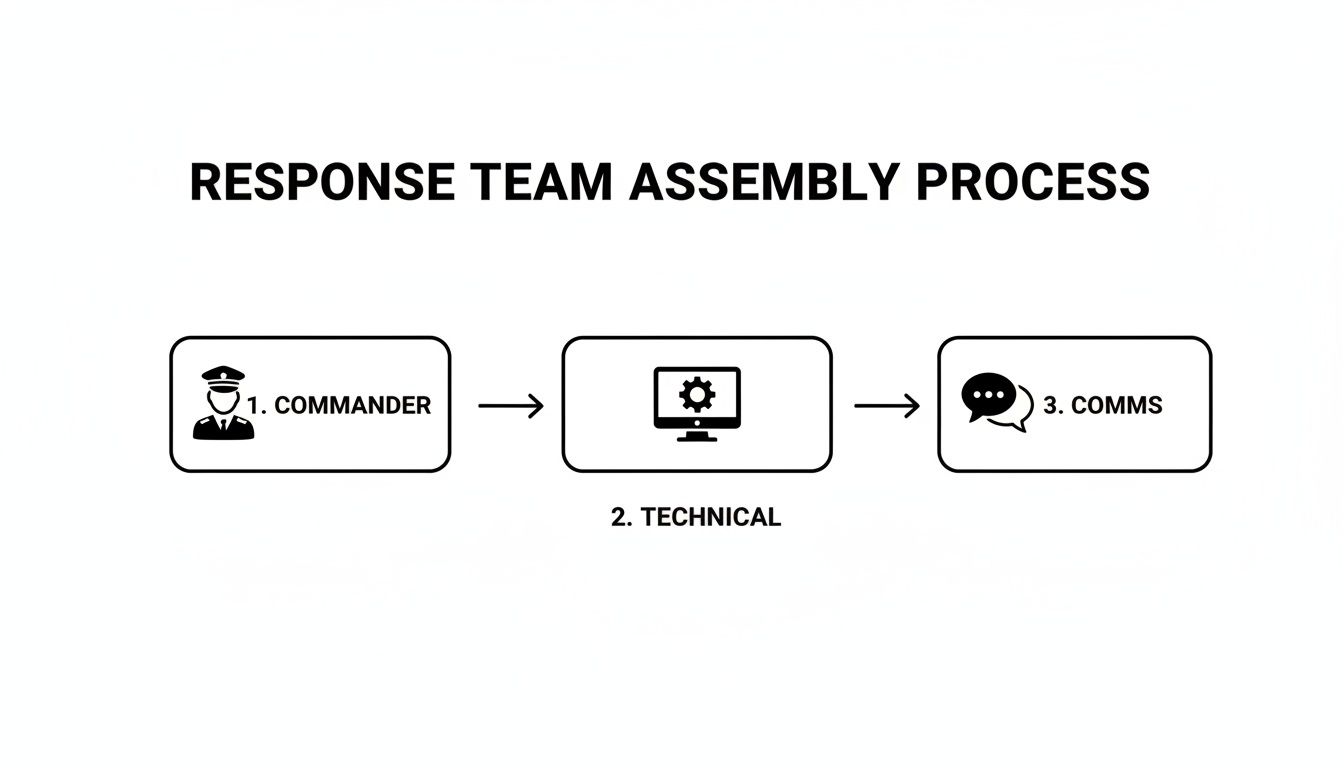
As you can see, a smooth response absolutely depends on coordinated action between leadership, your technical gurus, and the communications team.
The Fourth Phase: Post-Incident Recovery
The final phase starts once the immediate threat is gone. The goals here are to get operations back online safely and--just as important--to learn from what happened so it doesn't happen again.
Recovery means methodically bringing cleaned systems back online, verifying that they're running normally and, most importantly, securely. This shouldn't be a mad dash to get back to "business as usual." It needs to be careful and deliberate. According to Coveware, the average downtime from a ransomware attack is 24 days--but organizations with tested recovery plans reduce that figure by up to 50%.
After that comes the post-incident review, often called a "post-mortem." This is a blameless look back at the entire incident. The team gets together to talk through:
- What exactly happened, and what was the timeline?
- What did we do right during the response?
- Where did we struggle? What were the gaps in our process?
- How can we make our data breach response plan better?
- What metrics (MTTD, MTTR, total cost) can we benchmark for future improvement?
The takeaways from this meeting are pure gold. They get fed right back into updating security policies, sharpening procedures, and reinforcing defenses. This is the continuous improvement loop that turns a reactive incident response plan into a truly proactive security strategy.
5 Common Mistakes That Derail Data Breach Response Plans
- Treating the plan as a "set it and forget it" document. A 2024 SANS Institute survey found that 42% of organizations haven't updated their incident response plan in over 12 months. Threat landscapes change quarterly--your plan should too.
- Not including legal counsel from the start. Many organizations bring lawyers in only after the technical crisis is contained. By then, critical evidence may have been mishandled or notification deadlines missed. GDPR's 72-hour reporting window means legal needs to be at the table from minute one.
- Relying exclusively on IT for the entire response. Breaches are business events, not just technology events. Forrester research shows that organizations treating incident response as a cross-functional responsibility resolve breaches 33% faster than those who confine it to the IT department alone.
- Having no out-of-band communication plan. If your email servers are compromised, how will your team communicate? A CrowdStrike analysis found that 23% of ransomware incidents specifically targeted email and communication systems. Have a pre-arranged Signal group, satellite phone, or other backup channel ready.
- Skipping the post-mortem review. After the crisis subsides, there's enormous pressure to just "get back to normal." But the Ponemon Institute found that organizations conducting thorough post-incident reviews reduce the cost of subsequent breaches by an average of $280,000. The lessons learned are worth every hour invested.
Managing Communications and Legal Obligations
When a data breach hits, your technical response is only half the battle. How you communicate--what you say, when you say it, and who you say it to--is every bit as important. One wrong move with communications or a failure to meet your legal duties can turn a contained IT problem into a public relations disaster and a regulatory nightmare.
This is the point where your data breach response plan becomes a company-wide playbook, not just a document for the tech team. You absolutely need a clear, legally-vetted communications strategy to control the narrative, reassure everyone from your employees to your customers, and navigate the tangled web of notification laws. Getting your legal counsel involved from the very first minute isn't just a good idea--it's non-negotiable.
Crafting Your Communications Strategy
The goals are simple, but the execution is tough. You have to be transparent without causing a full-blown panic. You need to be timely without releasing information that hasn't been verified. A one-size-fits-all message just won't cut it, because every group you talk to has entirely different concerns. Edelman's 2024 Trust Barometer shows that 71% of consumers say they will permanently stop buying from a brand that they perceive has handled a data incident dishonestly.
Your plan needs a specific game plan for each audience:
- Internal Teams: Your employees are on the front lines. They need to hear what's going on from you, not from a news alert on their phone. Give them clear, simple facts about what happened and what it means for them and the company.
- Affected Customers: This is your most critical audience, and they need to be handled with care. Your communication has to be direct, empathetic, and genuinely helpful. Tell them exactly what data was compromised, what the risks are, and what concrete steps you're taking to protect them.
- Government Regulators: For regulators, it's all about speed and accuracy. Your legal team must quarterback this entire process to make sure you hit every reporting deadline and requirement, whether it's under GDPR, CCPA, or another framework.
- The Media and Public: All public statements should be funneled through your communications lead. The message must be consistent, factual, and project confidence that you have the situation under control.
"The heart of good crisis communication is owning your story. If you don't get out there quickly and transparently, someone else will fill the silence with speculation and rumor. Companies that acknowledge a breach within 24 hours and provide actionable next steps for affected individuals consistently retain more customer trust than those who delay."
-- Ann Cavoukian, Former Information and Privacy Commissioner of Ontario, creator of Privacy by Design
Navigating Complex Legal Requirements
The legal landscape for data breaches is a minefield, plain and simple. If you fail to comply with notification laws, you can get hit with staggering penalties that dwarf the initial cost of the breach itself. As of 2024, the United States continues to have the highest average cost of a data breach at $9.36 million (IBM). For "mega-breaches" affecting over 50 million records, costs can skyrocket, averaging an estimated $392 million.
The rules are all over the place, and they can vary dramatically:
- GDPR (General Data Protection Regulation): If you process data for anyone in the EU, the clock is ticking. You generally have just 72 hours to report a breach to the authorities after you become aware of it. In 2023 alone, European data protection authorities issued over $2.1 billion in GDPR fines.
- CCPA/CPRA (California Consumer Privacy Act/Privacy Rights Act): California's laws, like many other U.S. state laws, have their own notification timelines and specific requirements for what you have to say, often based on how many state residents were impacted. As of 2024, all 50 U.S. states now have some form of data breach notification law.
- Industry-Specific Regulations: If you're in a field like healthcare (think HIPAA) or finance (GLBA, PCI DSS), you're facing another layer of incredibly strict breach notification rules that have to be followed to the letter. HIPAA violations can carry fines of up to $2.13 million per violation category per year.
- SEC Cybersecurity Disclosure Rules (2023): Publicly traded companies in the U.S. must now disclose material cybersecurity incidents within four business days of determining materiality. This has fundamentally changed the speed at which public companies must act.
Your legal team's job is to map out all these overlapping obligations so that every action and every message is compliant. This is precisely why having pre-approved communication templates in your response plan is so critical--it lets you move fast without making a costly legal mistake under intense pressure. As you build out your plan, getting a handle on the broader privacy landscape is essential. You can read more about key privacy principles in our guide.
Ultimately, handling communications and legal duties well is about proving you're in control and taking responsibility. A well-executed strategy shows customers, regulators, and the public that you're a trustworthy steward of their data, even when things go wrong.
Download Your Customizable Response Plan Template
Knowing the theory behind incident response is one thing, but having a battle-tested plan in hand when a crisis hits is another entirely. This is where you get the central tool for your security arsenal--a complete and easily editable data breach response plan template.
This isn't just another generic document. It's a structured framework that I've seen teams adapt to their unique operational needs time and time again. The goal is simple: turn the advice in this guide into a tangible, crisis-ready asset so your team can act with confidence, not panic.
Our downloadable template is your first real step toward building that resilience.
What Is Inside the Template
I've made sure to pre-build all the essential sections so you can jump straight to customization instead of staring at a blank page. Think of it as a blueprint for your entire response process, designed to ensure nothing critical gets missed when the pressure is on.
Here's a look at what's included and ready for you to fill in:
- Response Team Contact List: A go-to directory for your Incident Commander, IT forensics, legal counsel, and communications leads. Crucially, it includes after-hours contact info because breaches don't stick to a 9-to-5 schedule.
- Role-Based Checklists: I've broken down actionable checklists for each DBRT member. These detail their specific duties during the critical containment, eradication, and recovery phases.
- Communication Drafts: Get a head start with pre-written communication templates for internal staff, your customers, and regulatory bodies. This helps ensure your messaging is clear, consistent, and legally sound from the first moment.
- Incident Logging Forms: Standardized forms are key for documenting every single action taken. This creates an undeniable timeline for post-incident analysis and proves compliance.
- Severity Classification Matrix: A pre-built matrix to help your team quickly categorize incidents by severity level (Low, Medium, High, Critical) with corresponding response time targets and escalation procedures.
A template provides structure in the midst of chaos. It ensures that critical actions, from legal notifications to technical containment, are guided by a pre-approved process, not panicked improvisation.
How to Customize Your Plan
A response plan is useless if it doesn't reflect your actual business environment. Our template is designed to be a living document--one that you mold to fit your company's size, industry, and the specific regulations you face.
Start by getting your Data Breach Response Team in a room to review and tailor each section. For example, a healthcare provider will need to heavily customize the legal and communications sections to meet strict HIPAA notification requirements. A small e-commerce business, on the other hand, might focus more on the customer support and payment processor notification checklists. Financial services firms will need to add specific sections for PCI DSS compliance and financial regulator notification.
After you've got a handle on the key components, you might also want to explore a complete incident response plan template to see another perspective. Gaining different insights as you refine your own document is always a good idea. The real objective here is to make the plan so familiar that executing it becomes second nature for your team.
Ready to get started? Download your free, customizable data breach response plan template now and take the most important step toward protecting your business.
Stop overpaying for AI tools you barely use. See how Dupple X helps your team adopt AI without the bloat.