Penetration testing in 2026 is being reshaped by two forces. AI-augmented pentesting tools (PentestGPT, PentAGI) moved from research to production-ready, with PentestGPT showing 228.6% task-completion improvement over baseline LLM in USENIX Security 2024 testing. Meanwhile, the cost floor for credible SMB pentests stayed at $4,000-$25,000 per engagement, and Burp Suite Professional raised its price to $499/year per user effective January 2026. See vulnerability assessment and penetration testing for more. See Open Source Intelligence (OSINT) for more. See Microsoft Azure for more. See Nmap for more. See pen testing market report from Grand View Research for more. See full penetration testing market analysis on Mordor Intell... for more.
The honest pentest landscape: you cannot replace a human pentester with an AI agent yet, but AI-augmented workflows let humans cover more ground in less time. Below is what penetration testing means in 2026, the standards that govern it, the tools and pricing, and how to scope an engagement without overpaying.
Quick reference: penetration testing in 2026
| Item | Detail |
|---|---|
| Standards | PTES, OWASP WSTG v4.2, NIST SP 800-115, OSSTMM 3 |
| SMB pentest cost | $4K-$25K typical, $5K-$20K external-only |
| Enterprise/continuous | $50K-$100K+ per year |
| Burp Suite Pro | $499/year per user (Jan 2026 price) |
| Cobalt Strike | ~$3,540/user/year |
| Top open source | Metasploit, Nuclei, OWASP ZAP, PentestGPT, PentAGI |
What penetration testing actually is
A simulated attack on your systems by an authorized tester, with the goal of finding exploitable vulnerabilities before a real attacker does. Five categories:
External network: Tests internet-facing infrastructure (web servers, VPN endpoints, mail servers).
Internal network: Tests assuming the attacker is already inside (compromised laptop, stolen credentials, insider threat).
Web application: Tests one or more specific web apps for OWASP Top 10 and business logic flaws.
API: Tests REST or GraphQL APIs for authentication, authorization, and injection issues.
Cloud (AWS/GCP/Azure): Tests cloud infrastructure for IAM misconfigurations, exposed storage, privilege escalation paths.
Most SMB engagements bundle external network plus web application. Most enterprise engagements bundle internal plus cloud plus continuous testing. See Amazon Web Services (AWS) for more. See Google Cloud Platform (GCP) for more.
What standards govern pentests
Four standards worth knowing:
PTES (Penetration Testing Execution Standard): The most widely used framework. Defines pre-engagement, intelligence gathering, threat modeling, vulnerability analysis, exploitation, post-exploitation, and reporting.
OWASP WSTG v4.2 (Web Security Testing Guide): The standard for web application pentests. Covers authentication, session management, input validation, business logic.
NIST SP 800-115: US federal standard for technical security testing. Required for some government contracts.
OSSTMM 3: Operational security testing methodology. Strong on metrics and reproducibility. Less common than PTES.
For most engagements: PTES for the overall framework, OWASP WSTG for web app testing depth.
Pick the right tools
The 2026 stack:
Open source (free):
- Metasploit: Exploit framework. The most popular pentest tool.
- Nuclei: Fast vulnerability scanner. Best for known-CVE detection at scale.
- OWASP ZAP: Web application proxy and scanner. Free alternative to Burp.
- PentestGPT: LLM-based assistant for pentest workflows. Open source.
- PentAGI: Autonomous multi-agent pentesting in Docker sandboxes. April 2026 release.
Commercial:
- Burp Suite Professional: $499/year per user (Jan 2026 price). The standard for web app pentesters.
- Burp Suite DAST (enterprise): ~$6,000/year. Continuous web app scanning.
- Cobalt Strike: ~$3,540/user/year. Red team operations and post-exploitation. Banned in some jurisdictions.
For most SMB pentests: Metasploit + Burp Suite Pro + Nuclei. For continuous testing: add PentAGI or commercial DAST.
Cost expectations for SMB pentests in 2026
Realistic ranges:
| Scope | Cost | Duration |
|---|---|---|
| External-only network pentest | $5K-$20K | 1-2 weeks |
| Web application pentest (one app) | $8K-$25K | 2-3 weeks |
| Internal network pentest | $10K-$30K | 2-4 weeks |
| Bundled external + web app | $15K-$40K | 3-4 weeks |
| Enterprise continuous pentest | $50K-$100K+/year | Ongoing |
What drives cost: scope size (number of IPs, web apps, APIs), depth of testing (vulnerability scan vs full exploitation), and remediation support included.
The mistake I see: SMBs paying $50K for a pentest that should cost $15K because they did not scope properly. Get 3 quotes. Specify scope clearly. Cheap quotes ($3K) usually mean automated scanning with a basic report, not a real pentest.
Bug bounty programs
Three platforms in 2026:
HackerOne: Largest researcher pool. Platform fees $30K-$150K/year plus bounty pool. Strong reputation, expensive.
Bugcrowd: Second-largest. Similar pricing. Good for managed programs.
Intigriti: European-focused. Often cheaper for European companies due to lower platform fees.
YesWeHack: Cheapest credible alternative. 20-40% lower than HackerOne for comparable scope.
Synack: Premium model with vetted researchers only. Highest cost. Best for compliance-driven programs.
For most SMBs: bug bounty programs are not the right starting point. Run pentests first. Add bug bounty when your application is mature enough that the residual vulnerabilities are subtle (which is when bounties earn their cost).
AI-augmented pentesting in 2026
Two production-ready tools:
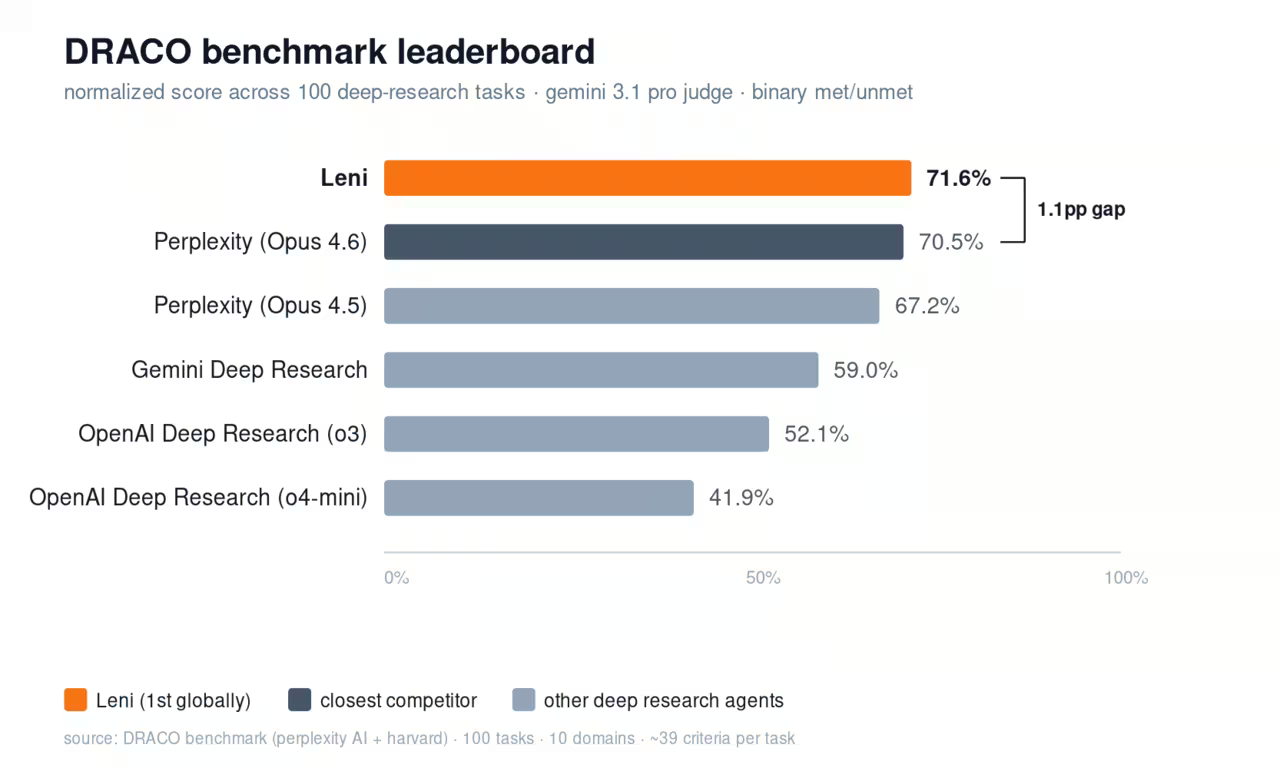
PentestGPT: Open source. USENIX Security 2024 reported 228.6% task-completion improvement over baseline LLM. Best for guided manual testing where the AI suggests next steps.
PentAGI: April 2026 release. Fully autonomous multi-agent pentesting in Docker sandboxes. Still requires human validation of findings, but reduces time-to-discovery for known vulnerability patterns.
What works in 2026: AI tools that augment human pentesters, automate reconnaissance, and suggest exploitation paths. The pentester reviews and validates.
What does not work: replacing the human pentester entirely. AI-only "fully autonomous pentests" miss business logic flaws, chained exploits, and context-specific vulnerabilities that humans catch.
How to scope a pentest engagement
Five questions to answer before getting quotes:
1. What systems are in scope? List specific IP ranges, web apps, APIs, cloud accounts.
2. What is out of scope? Production-only? Staging only? Specific domains excluded?
3. What is the testing methodology? PTES, OWASP WSTG, NIST? Specify.
4. What deliverables do you need? Executive summary, technical report, remediation guidance, retest after fixes?
5. What is the timeline? Most pentests run 2-4 weeks for fieldwork, 1 week for reporting.
The mistake I see: vague scope ("pentest our infrastructure") leading to vague quotes that double in cost mid-engagement. Specific scope produces accurate quotes.
What changed in 2025-2026
Three real shifts:
AI-augmented pentesting moved from research to production: PentestGPT (USENIX 2024) and PentAGI (April 2026) are both production-ready. Worth integrating into pentesters' workflows.
Burp Suite Pro raised prices to $499/year per user: Effective January 6, 2026. Still the standard for web app pentesters. Budget accordingly.
Continuous pentest pricing dropped: AI-augmented automation lowered the floor on continuous-pentest pricing. Some vendors now offer continuous monitoring at SMB price points ($30K-$50K/year).
FAQ
How much does a penetration test cost in 2026?
SMB engagements run $4K-$25K. External-only $5K-$20K. Web app $8K-$25K. Internal network $10K-$30K. Enterprise continuous testing $50K-$100K+/year. Get 3 quotes for any engagement.
What is the difference between a vulnerability scan and a pentest?
Vulnerability scans use automated tools (Nessus, Qualys, Nuclei) to flag known CVEs. Pentests use those tools plus human exploitation to confirm vulnerabilities are actually exploitable in your environment. Scans are cheap ($1K-$5K), pentests are real testing ($5K-$25K+).
Are AI-augmented pentest tools (PentestGPT, PentAGI) credible in 2026?
Yes for augmenting human pentesters. PentestGPT showed 228.6% task-completion improvement in USENIX 2024. PentAGI handles autonomous workflows in sandboxed environments. Both still require human validation. Full AI replacement of pentesters is hype.
Should I run a pentest or a bug bounty program?
Pentest first. Bug bounty later. Pentests find systemic issues. Bug bounties find subtle residual issues in mature applications. SMBs without prior pentests should not start with bug bounties.
What standards should my pentest follow?
PTES for the overall framework. OWASP WSTG v4.2 for web app testing depth. NIST SP 800-115 if required by federal contracts. Specify the standard in your scope so quotes are comparable.
Stop overpaying for AI tools you barely use. See how Dupple X helps your team adopt AI without the bloat.